A PSIM-class system is increasingly becoming the central tool for managing building security. It integrates various installations, organises alarms, supports operators and helps them make decisions during incidents. This is its greatest advantage — but also a source of risk.
The greater the influence a PSIM system has on building operations, the more important its resilience against errors, unauthorised access, uncontrolled changes and service disruptions becomes. That is why PSIM cybersecurity should not be treated as a project add-on. It is one of its foundations.
In practice, investors often ask what the system will integrate, what functions it will show the operator and how much it will streamline daily operations. The question of how to secure the PSIM platform itself — even though it is becoming the digital centre of security management — is asked far less often.
What is PSIM cybersecurity?
PSIM cybersecurity is a set of technical and organisational measures aimed at protecting the platform against unauthorised access, configuration errors, uncontrolled changes, data loss, disrupted communication with other systems and failures that prevent operators from working.
For an integration platform, it is not just about the server, the administrator password or antivirus software. Such a system connects multiple environments, processes numerous events and influences how people respond. For this reason, securing it must encompass architecture, access control, updates, activity monitoring and recovery procedures. In practice, such a platform operates as a PSIM-class system and should be designed with the operational continuity of the entire building in mind.
Why does PSIM cybersecurity matter so much?
A single domain-specific system is usually responsible for its own scope. PSIM works differently. It collects information from many sources, gives it context and presents the operator with a single picture of the situation.
This means that a problem in the PSIM platform can have consequences far wider than a failure of a single module. In practice, the following may all be at risk simultaneously: the reliability of information shown to the operator, the correctness of response procedures, the continuity of the security centre, the quality of cooperation between systems, and the ability to reconstruct event and action history. This is precisely why security system integration designed systematically — rather than as a collection of random connections — is so important.
From the building’s perspective, this is critical. If the security integration platform becomes unpredictable, the operator loses trust in the system. And that means even a well-designed integration can stop fulfilling its role. This issue is also well illustrated by the security paradox — a situation where an excess of signals and interfaces begins to burden staff rather than help them.
PSIM hardening — what does it mean in practice?
PSIM hardening means deliberately strengthening the system’s resilience. The goal is to prepare the environment so as to reduce the attack surface, simplify the architecture, remove unnecessary components and introduce control over access and changes.
In practice, PSIM hardening includes network segmentation, restricting access to essential personnel, separating user roles, disabling unnecessary services and ports, controlled updates, logging administrative actions, backups and recovery testing.
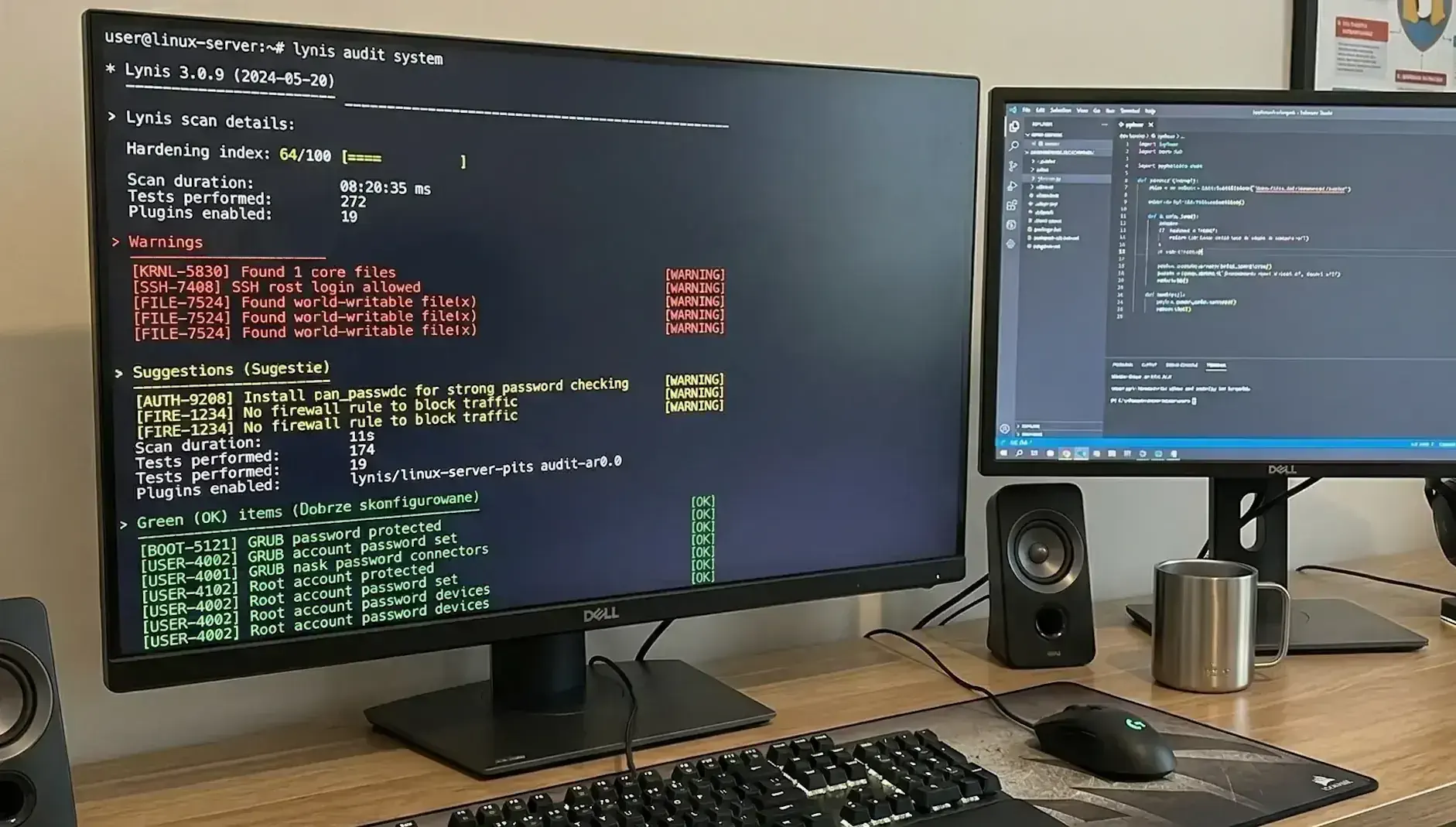
This is not a topic for the IT department at the end of deployment. It is part of the responsible design of a platform intended to support the security of the entire building. A useful starting point is Lynis, a tool that automatically audits server configuration and highlights specific areas for hardening. It is also worth consulting the CIS Benchmarks — free, detailed hardening guides published by the CIS organisation for specific operating systems, databases and server platforms.
The most common mistake: treating PSIM like an ordinary application
In many buildings, the PSIM system is deployed as if it were ordinary utility software. It is expected to start up, display events and connect to other systems. The problem is that this logic is far too simplistic.
PSIM is not an ordinary office application. It is a platform that operates at the intersection of physical security, network infrastructure, operational procedures, technical maintenance and decisions made under time pressure. For many buildings, it is only through security system integration that this area can be organised — but only when new digital vulnerabilities are not introduced in the process.
This is precisely why a poorly secured PSIM can be more dangerous than no integration at all. It creates an illusion of central control, while in reality it may be vulnerable to errors, misuse or organisational chaos.
7 PSIM hardening principles
1. Network segmentation for the PSIM system
The first principle is to isolate the PSIM environment from the regular office network. A platform that integrates building security should not operate in the same flat network space as user workstations, printers or services unrelated to security.
A well-prepared architecture should limit communication exclusively to necessary connections. Every additional port, uncontrolled access point and every temporary exception increases risk. Practical guidance on closing unnecessary services, port knocking and log monitoring can be found in this Linux server hardening guide on Sekurak.pl (in Polish).
2. Separate accounts and clear user roles
In PSIM systems, there should be no room for shared operator logins or anonymous administration. Every user should have their own account, and their permissions must reflect their actual role.
This is especially important because a PSIM system affects many building functions. A single erroneous change can produce consequences far wider than in an individual domain-specific system.
3. Strong authentication and remote access control
Administrative access to the PSIM system should be protected more robustly than a standard operator account. This applies in particular to administrators, service personnel, remote access, databases and privileged accounts.
Most risks typically arise not where the system is used daily, but where exceptions have been left in place: an installation account, broad service access or a remote connection launched without supervision.
4. Reducing the attack surface
One of the fundamental hardening principles is simple: if something is not needed, it should not be running.
In a PSIM environment, it is worth removing or disabling unused modules, default accounts, unnecessary services, legacy integration components, unneeded remote connections and test functions left over from deployment. The simpler the environment, the greater the predictability and the lower the risk. On Windows-based operator workstations, a tool like Hardentools (article in Polish) can automatically disable system features commonly exploited by attackers.
5. Controlled PSIM updates
PSIM updates should not be carried out haphazardly. Every change can affect not only the platform itself, but also integrations, databases, operator workstations and user workflows.
A structured process is therefore needed — one that includes impact assessment, testing, a deployment plan, the ability to roll back the update and accountability for change approval. Lack of updates is a problem. But an update carried out without control can be equally dangerous.
6. Logging activity in the PSIM system
In a well-secured PSIM, recording alarms alone is not enough. You also need to know who logged in, who attempted to log in unsuccessfully, who changed the configuration, who granted or revoked permissions, who initiated a remote service session and when communication errors occurred.
Only then can you distinguish an ordinary failure from a user error or a deliberate action.
7. Backup and PSIM recovery
Backups are important, but in practice what matters more is whether a working system can be quickly restored from them.
For PSIM, you need to back up not only the database, but also the configuration, maps, visualisations, operator procedures, user roles, communication settings and integration components. It is equally important to test how long recovery actually takes and who is responsible for each stage.
PSIM security is also an organisational issue
This topic is often overlooked. Even a well-designed system can be weakened by a poor division of responsibilities. If it is unclear who approves changes, who has administrative access, who is responsible for updates, who analyses logs and who initiates the recovery procedure, then PSIM cybersecurity begins to depend on habits rather than rules. In practice, this kind of organisational disorder is often one of the main causes of problems — not because the technology is weak, but because no one manages it coherently. This is also well illustrated by the perspective of shared responsibility for building security, especially where different disciplines and procedures meet.
What are the benefits of a well-secured PSIM system?
A properly secured PSIM system gives a building more than just protection against cyberattacks. It also provides greater operational stability, better control over changes, higher predictability for operators, lower risk of errors, greater trust in the information presented by the system and better resilience against failures and incidents.
This matters wherever security cannot rely on guesswork and improvisation. In practice, dual alarm verification also helps — linking events to spatial context, cameras and the logic of operator actions.
Summary
If a PSIM system is to genuinely support building security, it must itself be properly secured. It is not enough that it integrates many installations and looks good on the operator’s workstation.
What counts is whether it runs in an isolated environment, has controlled access, limits unnecessary functions, allows changes to be tracked, is updated in a structured manner and can be recovered after a failure. In this context, the continuity of infrastructure operations is equally important, because without a stable technical foundation even the best platform will not fulfil its role.
PSIM cybersecurity is not a side issue. It is one of the conditions that determine whether the platform truly increases the building’s level of security — or merely creates that impression.
FAQ
Does a PSIM system require a separate approach to cybersecurity?
Yes. PSIM integrates multiple systems and affects how operators respond, so its security should be treated more broadly than that of an ordinary application.
What does PSIM hardening involve?
Hardening involves strengthening the system's resilience through network segmentation, access restriction, disabling unnecessary services, update control, activity monitoring and preparing recovery procedures.
What are the most common mistakes when securing PSIM?
The most common issues are lack of network segmentation, shared user accounts, leftover service accounts, uncontrolled remote access, no recovery testing and weak change control.
Is a PSIM backup enough to ensure security?
No. A backup alone is not sufficient. You also need to be able to effectively and quickly restore a working system — including its configuration, integrations and operator procedures.
Who should be responsible for PSIM security?
It is a shared responsibility. The building owner, security department, technical maintenance, the integrator and administrators should all have clearly defined roles and operating rules.